-
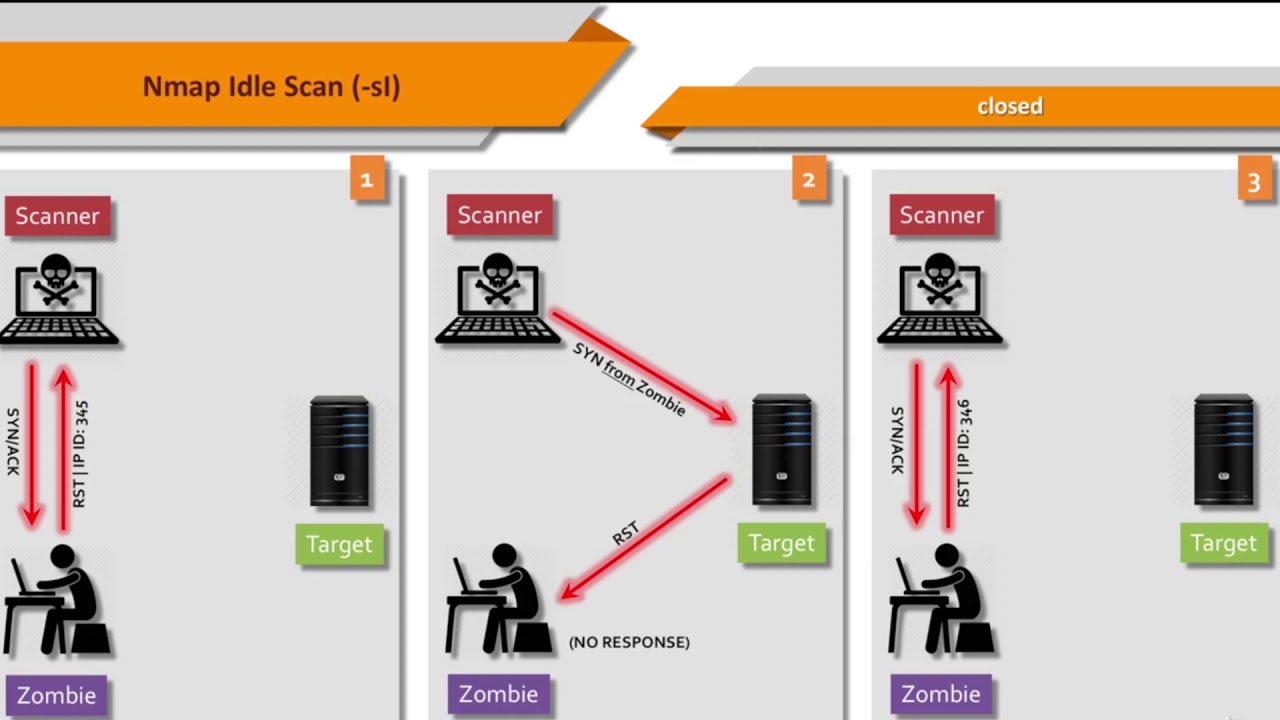
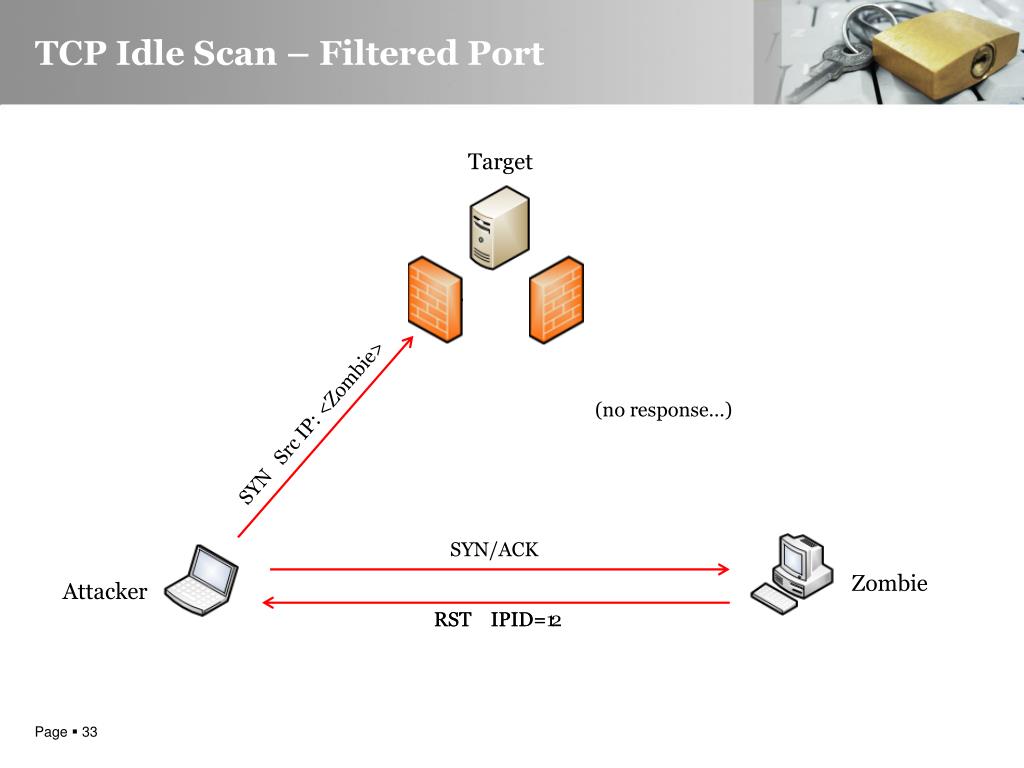 PPT - Advanced Idle Scanning PowerPoint Presentation, download - ID:5241398
PPT - Advanced Idle Scanning PowerPoint Presentation, download - ID:5241398
ID: uU7xx60j34
From:
-
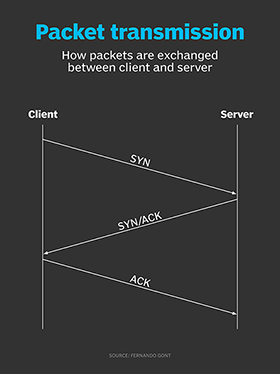
 What is Idle Scan? | ICterra Communication
What is Idle Scan? | ICterra Communication
ID: iBLbSRsGLP
From:
-
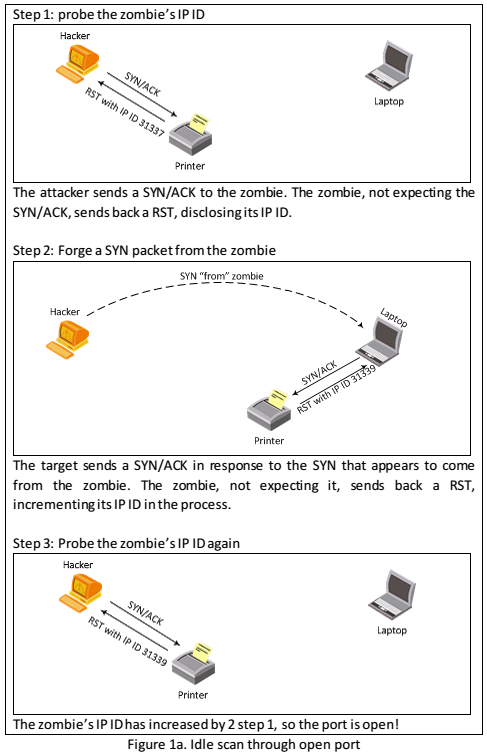
 How hackers use scans in port scan attacks | TechTarget
How hackers use scans in port scan attacks | TechTarget
ID: fqTdZj3tcT
From:
-
 Figure 13 from Master s Thesis TCP Idle Scans in IPv 6 | Semantic Scholar
Figure 13 from Master s Thesis TCP Idle Scans in IPv 6 | Semantic Scholar
ID: bw4SqUNjos
From:
-
 How hackers use scans in port scan attacks | TechTarget
How hackers use scans in port scan attacks | TechTarget
ID: vbrSpJGeBv
From:
-
 scan - Wikipedia
scan - Wikipedia
ID: 5XYpCf6niH
From:
-
 Nmap Scan tutorial
Nmap Scan tutorial
ID: BhXaZDEDXo
From:
-
 What is Idle Scan? | ICterra Communication
What is Idle Scan? | ICterra Communication
ID: qSJVuGoMSy
From:
-
 Antivirus Idle Scan takes a while to stop - ESET Endpoint Products Security Forum
Antivirus Idle Scan takes a while to stop - ESET Endpoint Products Security Forum
ID: auqG1uTY2M
From:
-
 Nmap cheat sheet: discovery to exploits, part 2: port scanning with Nmap and idle scan Infosec Resources
Nmap cheat sheet: discovery to exploits, part 2: port scanning with Nmap and idle scan Infosec Resources
ID: fcwb4T4Oqe
From:
-
– Idle Scan | Linux.org
ID: vuwOa5YM6y
From:
-
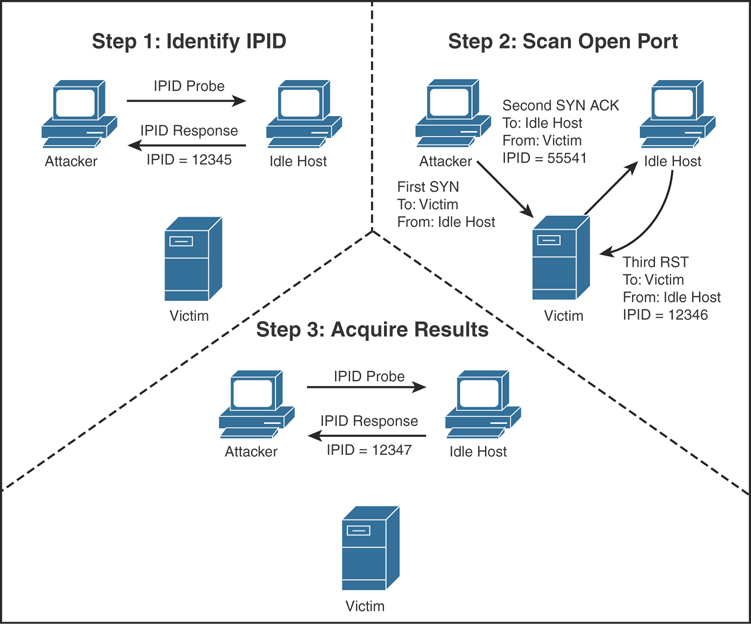
 TCP Idle Scan in IPv4 Download Diagram
TCP Idle Scan in IPv4 Download Diagram
ID: zXenuglYD0
From:
-
 Scan - YouTube
Scan - YouTube
ID: KOzSjuQKO8
From:
-
 Port | Infosec Resources
Port | Infosec Resources
ID: zZgp29ROoY
From:
-
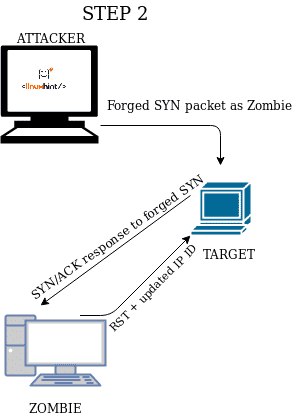
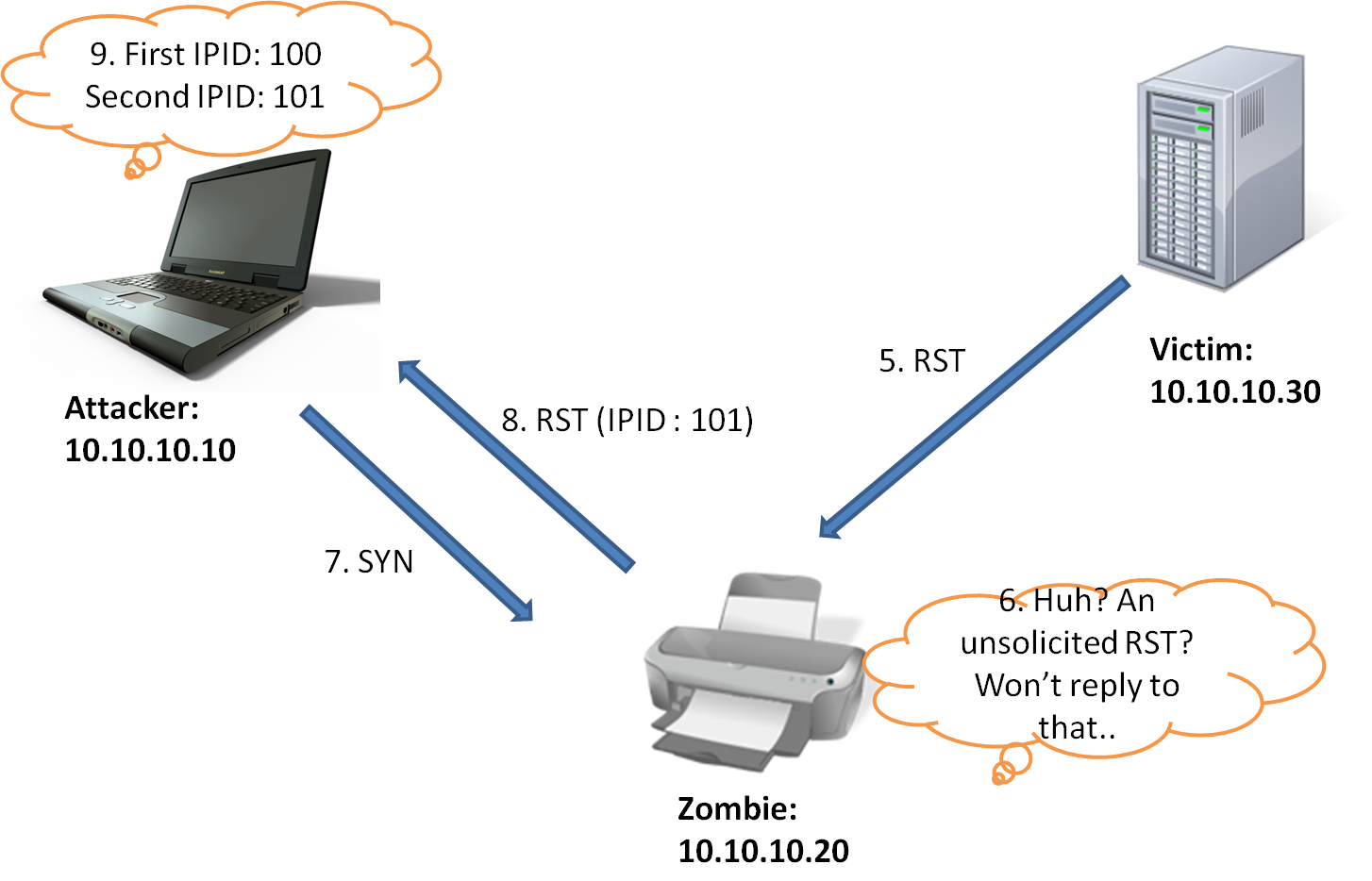
 Zombie/Idle scan working | by NGU |
Zombie/Idle scan working | by NGU |
ID: XxrnQAai1D
From:
-
 Figure 8 from Master s Thesis TCP Idle in 6 | Scholar
Figure 8 from Master s Thesis TCP Idle in 6 | Scholar
ID: Fy39x4vdNY
From:
-
 TCP Idle Scan in IPv4 with Nmap | Download Diagram
TCP Idle Scan in IPv4 with Nmap | Download Diagram
ID: 6F5k2ZHFe4
From:
-
 Performing Nmap Idle
Performing Nmap Idle
ID: 7H5cu0KDzO
From:
-
 Scanning | Reconnaissance, and | Pearson IT Certification
Scanning | Reconnaissance, and | Pearson IT Certification
ID: 8PVYbXndoC
From:
-
 scan - Guide
scan - Guide
ID: HKKsYPS9wF
From:
-
 scan - Wikipedia
scan - Wikipedia
ID: 6pCbDSsgVv
From:
-
 Vipul Blog: How does idle scan work?
Vipul Blog: How does idle scan work?
ID: C31vGPPNhK
From:
-
 Reconnaissance- Idle Scan YouTube
Reconnaissance- Idle Scan YouTube
ID: 0i0bZjVJbX
From:
-
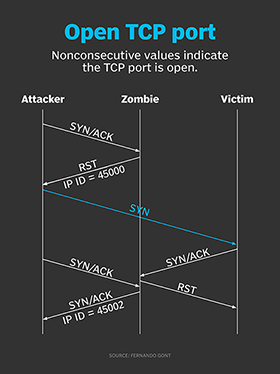 How hackers use scans in port scan attacks | TechTarget
How hackers use scans in port scan attacks | TechTarget
ID: fVwHG7nez2
From:
-
– Idle Scan | Linux.org
ID: NuNOwh7TpC
From: